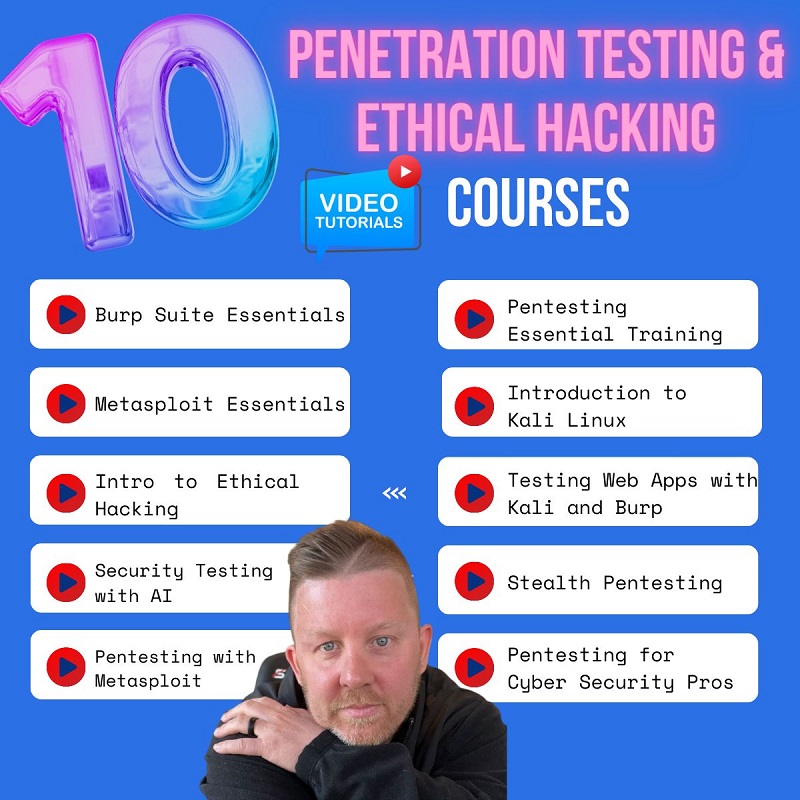
Fundamentals concepts on Security Policies and Access Control in Computer Security
Terms-Computer security, network security, Internet security, and information security are interchangeably used in the fields of security in computing.
The computer security is the generic name for the collection of tools designed to protect data and to thwart hackers, the network security measures needed to protect data during their transmission, the Internet security measures to protect data during their transmission over a collection of interconnected networks.
Internet security consists of measures to deter, prevent, detect, and correct security violations that involve the transfer and storage of information whereas the information security refers to the processes and methodologies which are designed and implemented to protect print, electronic, or any other form of confidential, private and sensitive information or data from unauthorized access, use, misuse, disclosure, destruction, modification, or disruption.
Confidentiality, integrity, and availability are the most fundamentals concept of information security. The secrecy ensures that computer-related assets are accessed only by the authorized party. Integrity means that assets can be modified only by authorized parties or just in approved ways. Availability means that assets are accessible to authorized parties at the appropriate time
A security policy is a statement of what is and what is not, allowed. The security policy defines “security “for the site or system, and the plan can be formal or informal. A security mechanism is a method, tool, or procedure for enforcing a security policy. A security model is a model that represents a particular policy or set of plans. A confidentiality policy is a security policy dealing only with confidentiality.
An integrity policy is a security policy dealing only with integrity. The security policies (M. Bishop) can be classified into two classes- military security policies and commercial security policy. The military security policies are defined as primarily concerned with preserving information confidentiality while commercial security policies primarily focus on guaranteeing information integrity.
Access control is a mechanism by which a system grants or revokes the right to access some objects (files or data) or perform some action on the system.
Mandatory Access Control (MAC)
Under a MAC enforced environment access to all resource objects such as data files is controlled by settings defined by the system administrator. As such, all access to resource objects is strictly controlled by the operating system based on system administrator configured settings.
It is not possible under MAC enforcement for users to change the access control of a resource.
Mandatory Access Control begins with security labels assigned to all resource objects on the system that is top secret, confidential etc.
Similarly, each user account on the system also has classification and category properties from the same set of features applied to the resource objects. When a user attempts to access a resource under Mandatory Access Control, the operating system checks the user’s classification and categories and compares them to the properties of the object’s security label.
If the user’s credentials match the MAC security label properties of the object access is allowed. It is important to note that both the classification and categories must match. A user with top-secret classification, for example, cannot access a resource if they are not also a member of one of the required categories for that object.
Mandatory Access Control is by far the most secure access control environment but does not come without a price. Firstly, MAC requires a considerable amount of planning before it can be effectively implemented.
Once implemented it also imposes a high system management overhead due to the need to constantly update object and account labels to accommodate new data, new users and changes in the categorization and classification of existing users.
Discretionary Access Control (DAC)
Unlike Mandatory Access Control (MAC) where access to system resources is controlled by the operating system (under the control of a system administrator), Discretionary Access Control (DAC) allows each user to control access to their own data. DAC is typically the default access control mechanism for most desktop operating systems.
Instead of a security label in the case of MAC, each resource object on a DAC based system has an Access Control List (ACL) associated with it. An ACL contains a list of users and groups to which the user has permitted access together with the level of access for each user or group.
It is important to note that under DAC a user can only set access permissions for resources which they already own. A hypothetical User A cannot, therefore, change the access control for a file that is owned by User B. User A can, however, set access permissions on a file that she owns. Under some operating systems it is also possible for the system or network administrator to dictate which permissions users are allowed to set in the ACLs of their resources.
Discretionary Access Control provides a much more flexible environment than Mandatory Access Control but also increases the risk that data will be made accessible to users that should not necessarily be given access.
Roles differ from groups in that while users may belong to multiple groups, a user under RBAC may only be assigned a single role in an organization.
Additionally, there is no way to provide individual users additional permissions over and above those available for their role. The accountant described above gets the same permissions as all other accountants, nothing more and nothing less.
Rule-Based Access Control
Rule-Based Access Control (RBAC) introduces acronym ambiguity by using the same four-letter abbreviation (RBAC) as Role Based Access Control.
Under Rules Based Access Control, access is allowed or denied to resource objects based on a set of rules defined by a system administrator. As with Discretionary Access Control, access properties are stored in Access Control Lists (ACL) associated with each resource object. When a particular account or group attempts to access a resource, the operating system checks the rules contained in the ACL for that object.
Author: Dilli Sharma