From 26th October 2016 to 30th October 2016 IT-Training Nepal (ITN) is going to conduct Penetration Testing Training in Nepal. Within these five days, training courses you learn about penetration testing in detail. So hurry up to grab this opportunity.
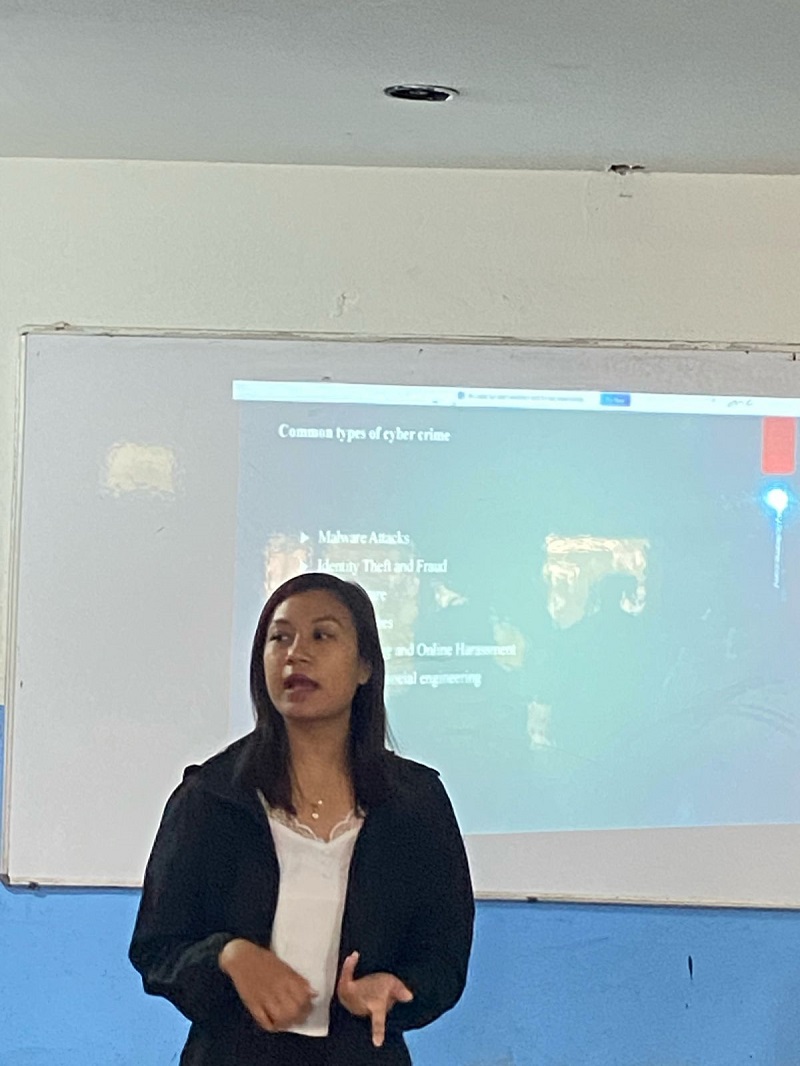
Now the importance of the security is rapidly increasing day by day, in case of network it is the most crucial, so the concept of penetration testing training has been developed. Here, the objectives of the CEH are completely covered along with topics like Kali Linux and Pen Testing Standards like NSA IAM, PCI, NIST 800-115, NIST 800-53 A, etc.
Not only this, Google Hacking and Use of ShodanHQ are also covered. Besides, students are also prepared to pass the professional penetration tester certification test, i.e., http://www.professionalpentester.com/.
Here students learn on the basis of these topics:
- Penetration testing standards
- NSA IAM
- PCI
- NIST 800-115
- NIST 800-53 A
- Scanning
- Details of scan types
- Very detailed on map
- Detailed on shodanhq
- Detailed on ‘Google Hacking’
- OS enumeration
- Account enumeration
- tcpdump
- Windows hacking
- Detailed use of net and netsh
- Coverage of Windows passwords
- Common Windows hacking techniques
- Malware creation
- Using terabit
- Using elite wrap
- Batch viruses
- Powershell viruses
- Netcat as a reverse shell/trojan
- Linux/Kali
- Basic Linux
- Use of Vega
- Use of Recon-ng
- Use of Dmitry
- Other tools at class request or instructor’s discretion
- Crypto
- Basic overview
- Windows NTLM
- Pass the hash
- Hashing
- Rainbow tables
- Password cracking
- Web hacking
- SQL Injection in detail
- Cross-site scripting (including necessary JavaScript)
Students will also have hands-on labs where they will learn to:
- Create basic malware
- Use shodanhq effectively
- Use map effectively
- Use Kali Linux effectively
- Do SQL injection
- Do cross-site scripting
So come forward and do some learning task on penetration testing courses to secure our network security.