Phishing Attacks Carried out using Chipotle’s Marketing Account
1st August 2021, Kathmandu
Customers’ payment card data was stolen by hackers using malware planted at the great majority of Chipotle Mexican Grill’s more than 2,000 locations, according to the restaurant business.
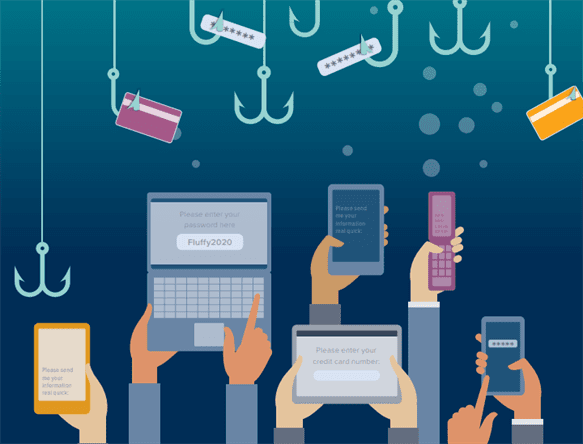
The email marketing account belonging to the American fast-food chain Chipotle Taco used its phishing campaign. The attacker sends a phishing email to induce the target to click on a malicious link.
Almost all messages lead potential victims to credential collection sites masquerading as banking organizations and technology companies Microsoft services. Fortunately, there are very few phishing emails with malware attached.
How did the Chipotle phishing attack happen?
During a phishing operation, a hacked Mailgun account used by a US company for email marketing purposes sent more than 120 malicious emails.
Attacks can be successful with a real email address, especially if you have an automatic protection solution to verify that your email address passes Domain Key Recognized Mail (DKIM) authentication Methodology and sender policy framework. It is critical to understand that it is feasible.
Most messages are Microsoft messages designed to collect login information from the recipient. In a blog post, email security company Inky stated that it has detected 105 such emails in the last three days of phishing operations.
Almost everyone has a Microsoft account. Logging in can provide you with all kinds of interesting data, including other login information, company secrets, financial details, and other intelligence. According to Bleeping Computer, the email appeared to be from the “Microsoft 365 Message Center” and notified the victim that an email could not be sent “due to insufficient email storage space in the cloud.”
Therefore, when a user clicks a button that appears to “send a message to their inbox”, they are immediately redirected to a fake Microsoft login page that collects sensitive data. The attackers also disguised themselves as the United Service Automobile Association (USAA), a diversified Fortune 500 financial services group in San Antonio. Banking, investing, and investing in people who have worked or worked in the United States and family army.
The email security company did not disclose the threats provided, but the business email breach (BEC) scammers provided information theft programs to collect data that could be used for the social engineering part of the fraud.
Inky researchers stated that there is no indication that the latest phishing operation was carried out by the same threat actors.
It’s also unknown, at least to INKY, where the phishing assault originated. “Because these emails came through Mailgun servers, we have no idea who is behind this attack or where they are,” Alibe explained.
After “work anywhere, anytime” in 2020, many companies have felt the loss of employees working remotely, who often use unsecured personal devices owned by the company to access SaaS services. Organizations must incorporate anti-phishing and identity protection technologies into their security policies.