Computer Hacking was suddenly more real than ever
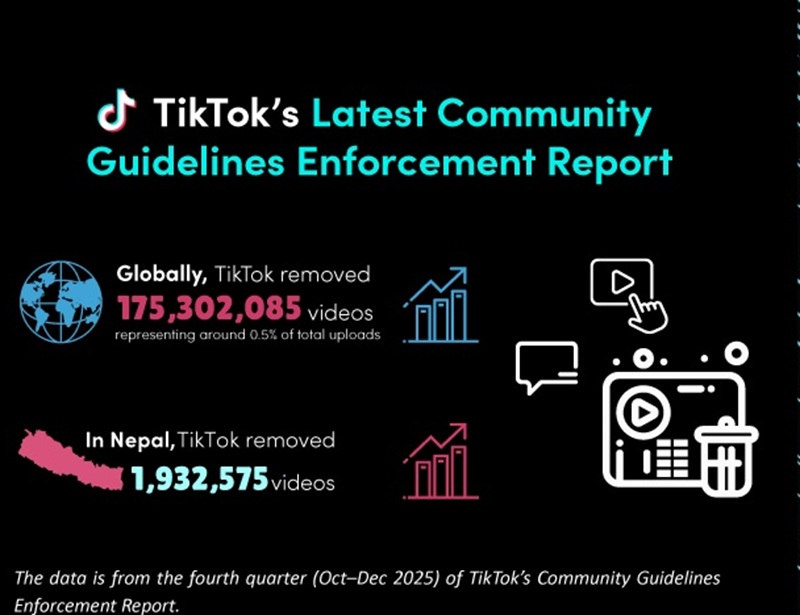
There are currently more than 10 billion internet-connected devices, and what people do to make sure that their information stays secure?
With the new generation of technology and the internet, the number of hackers has also risen. In the early 1980s with people buying personal computers for their home and work, the generation of hacker has begun.
Hacking and system cracking is like a new trend in this generation. Some break into computer networks for money and some for revenge but these curious kids tapped into whatever computer system they could find just to explore. In Washington DC, a teenager accidentally touches into a military computer and nearly brought the world to nuclear war. In 2000, the ‘I LOVE YOU’ worm, also known as VBS/Love letter and Love Bug worm, is a computer worm written in Vb Script.
It infected millions of computers worldwide within a few hours of its release. It is considered to be one of the most damaging worms ever. It originated in the Philippines; made by an AMA Computer College student for his thesis.
The computer security threats: Hacking and System Cracking has started getting more severe kind of damage for any individual or organization. In 1990, hacker Kevin Paulsen rigged a Los Angeles radio station’s phone system to win a Porsche but was arrested afterward. Even millions of dollars have been stolen by hackers from banks with the most robust security.
Nationwide fears for computer security and threats have led them to pass the Computer Fraud and Abuse Act, Information Technology Act, Electronic Act, Cyber Law, etc. because breaking into a computer system is now a crime of its own.
The game of cat-and-mouse between law enforcement and hackers continued throughout the 1990s. But pirates are still more of an annoyance than anything devastating, the stock market, banking transaction, trading, and others – everything is running on computers now. The number of people online will double to five billion by the end of this decade, and the problems of hacking and system are cracking will continue throughout the globe, for which digital policy must be designed for the twentieth century and begin to meet the challenges of this digital age successfully.