Cybercriminals Abusing Internet-Sharing Services to Monetize Malware Campaigns
3rd September 2021, Kathmandu
Threat actors are capitalizing on the growing popularity of proxy war platforms like Honeygain and Nanowire to monetize their own malware campaigns, once again illustrating how assailants are expeditious to repurpose and weaponize legitimate platforms to their advantage.
“Malware is currently leveraging these platforms to monetize the cyber world bandwidth of victims, kindred to how malignant cryptocurrency mining endeavors to monetize the CPU cycles of infected systems,” researchers from Cisco Talos verbally expressed in a Tuesday analysis. “In many cases, these applications are featured in multi-stage, multi-payload malware attacks that provide adversaries with multiple monetization methods.”
Proxyware, withal called internet-sharing applications, are legitimate accommodations that sanction users to carve out a percentage of their cyberspace bandwidth for other contrivances, often for a fee, through a client application offered by the provider, enabling other customers to access the cyber world utilizing the cyber world connections offered by nodes on the network. For consumers, such accommodations are “advertised as an expedient to circumvent geolocation checks on streaming or gaming platforms while engendering some income for the utilizer offering up their bandwidth,” the researchers expounded.
But the illicit utilization of proxy war withal introduces a multitude of perils in that they could sanction threat actors to obfuscate the source of their assailants, thereby not only giving them the competency to perform malignant actions by making it appear as if they are originating from legitimate residential or corporate networks but additionally render ineffective conventional network bulwarks that rely on IP-predicated blocklists.
“The same mechanisms currently used to monitor and track Tor exit nodes, “innominate” proxies, and other prevalent traffic obfuscation techniques do not currently subsist for tracking nodes within these proxy wars networks,” the researchers noted.
That’s not all. Researchers identified several techniques adopted by deplorable actors, including trojanized proxy war installers that sanction for surreptitious distribution of information purloiners and remote access trojans (RATs) without the victims’ erudition. In one instance optically canvassed by Cisco Talos, assailers were found utilizing the proxy war applications to monetize victims’ network bandwidth to engender revenue as well as exploit the compromised machine’s CPU resources for mining cryptocurrency.
Another case involved a multi-stage malware campaign that culminated in the deployment of an info-purloiner, a cryptocurrency mining payload, as well as proxy wars software, underscoring the “varied approaches available to adversaries,” who can now transcend cryptojacking to additionally plunder valuable data and monetize prosperous infections in other ways.
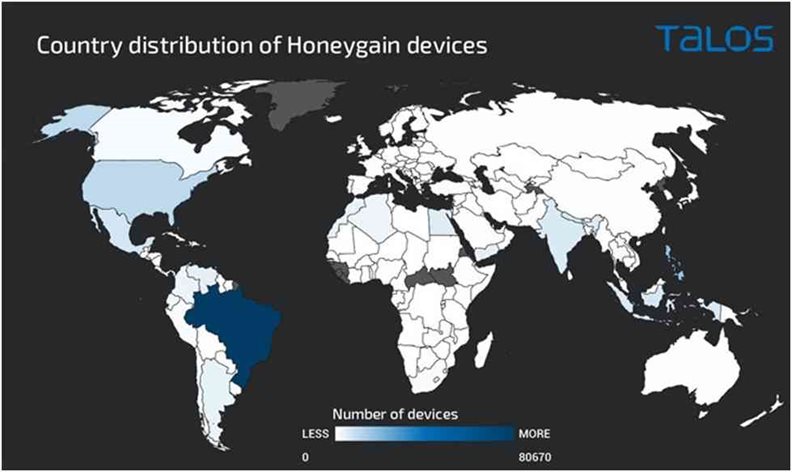
Even more concerningly, researchers detected malware that was acclimated to mutely install Honeygain on infected systems, and register the client with the adversary’s Honeygain account to profit off the victim’s internet bandwidth. This additionally betokens that an assailer can sign up for multiple Honeygain accounts to scale their operation predicated on the number of infected systems under their control.
“For organizations, these platforms pose two essential quandaries: The abuse of their resources, ineluctably being blocklisted due to activities they don’t even control and it increments organizations’ assailment surface, potentially engendering an initial attack vector directly on the endpoint,” the researchers concluded. “Due to the sundry risks associated with these platforms, it is recommended that organizations consider proscribing the utilization of these applications on corporate assets.”