Data Security Is A Risk Management Problem
The significant database vulnerabilities that are present today for more than a decade ago are buffer overflows and SQL injection. These vulnerabilities provide access for the attackers who may compromise the database systems and workarounds and patches may exist. The breachers could also get their way to the system by using default user account names and passwords; thus the cost of providing user accounts is high according to IT professionals and database administers. Through the public breach disclosure, it is clear that unencrypted tapes are lost or sensitive data moved to unsecured systems regularly.
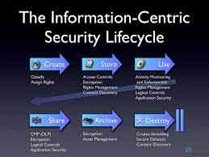
To improve the data security management of an organization, the organization must focus on the need for clear, actionable and pragmatic method rather than fancy encryption methods, forensic analysis or event correlation. But the necessary factors are overlooked sometimes in a large company or organization, and this appears to be disadvantageous to database professionals who don’t know where to begin.
Everyone wants to perform their task most simply. Here are some techniques that could help to provide data protection, cover database configuration, account provisioning, OS/ database interaction and considerations for front-end applications that use the database. If these techniques are not considered many significant database security measures becomes just a waste of time.
Here are some lists of data security management measures:
Access controls and Authorization steps
Access database configuration
Access database/ platform interaction
Secure communications
Patching database
Application usage of the database
Media protection
Log and Event Review
Embrace Insecurity