PwnedPiper PTS Security Imperfections Threaten 80% of Hospitals in the U.S.
3rd August 2021, Kathmandu
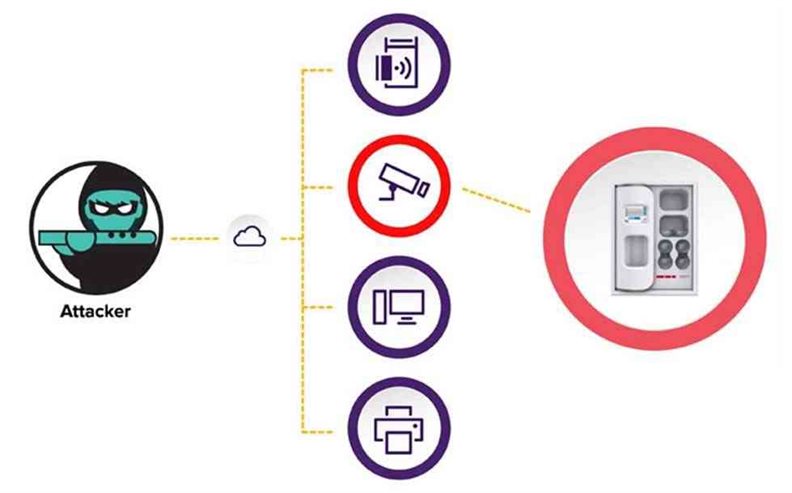
Cybersecurity researchers on Monday disclosed a set of nine susceptibilities kenned as “PwnedPiper” that left a widely-used pneumatic tube system (PTS) vulnerably susceptible to critical attacks, including a possibility of a consummate takeover.
The security impotence, disclosed by American cybersecurity firm Armis, impacts the Translogic PTS system by Swisslog Healthcare, which is installed in about 80% of all major hospitals in North America and in no fewer than 3,000 hospitals ecumenical.
“These susceptibilities can enable an unauthenticated assailer to surmount Translogic PTS stations and essentially gain consummate control over the PTS network of a target hospital,” Armis researchers Ben Seri and Barak Hadad verbalized. “This type of control could enable sophisticated and worrisome ransomware attacks, as well as sanction assailers to leak sensitive hospital information.”
Pneumatic tube systems are internal logistics and convey solutions that are habituated to convey blood samples in hospital settings to diagnostic laboratories securely.
Prosperous exploitation of the issues, consequently, could result in leakage of sensitive information, enable an adversary to manipulate data, and even compromise the PTS network to carry out a man-in-the-middle (MitM) attack and deploy ransomware, thereby efficaciously halting the operations of the hospital.
The details about the nine PwndPiper susceptibilities are listed as follows –
- CVE-2021-37161 – Underflow in udpRXThread
- CVE-2021-37162 – Overflow in sccProcessMsg
- CVE-2021-37163 – Two hardcoded passwords accessible through the Telnet server
- CVE-2021-37164 – Off-by-three stack overflow in tcpTxThread
- CVE-2021-37165 – Overflow in hmiProcessMsg
- CVE-2021-37166 – GUI socket Denial of Accommodation
- CVE-2021-37167 – Utilizer script run by root can be utilized for PE
- CVE-2021-37160 – Unauthenticated, unencrypted, unsigned firmware upgrade
In a nutshell, the imperfections — which concern privilege escalation, recollection corruption, and denial-of-accommodation — could be abused to gain root access, achieve remote-code-execution or denial-of-accommodation, and worse, sanction an assailant to maintain sedulousness on compromised PTS stations via an insecure firmware upgrade procedure, leading to unauthenticated remote-code-execution. It’s additionally worth noting that a patch for CVE-2021-37160 is expected to be shipped at a future date.
“The potential for pneumatic tube stations (where the firmware is deployed) to be compromised is dependent on a deplorable actor who has access to the facility’s information technology network and who could cause supplemental damage by leveraging these exploits,” Swisslog Healthcare verbally expressed in an independent advisory published today.
Translogic PTS system customers are highly recommended to update to the latest firmware (Nexus Control Panel version 7.2.5.7) to mitigate any potential risk that may arise out of genuine-world exploitation of the shortcomings.
“This research illuminates systems that are obnubilated in plain visual perception but are nevertheless a crucial building block to modern-day healthcare,” Seri and Hadad verbally expressed. “Understanding that patient care depends not only on medical contrivances, but additionally on the operational infrastructure of a hospital is a consequential milestone to securing healthcare environments.”