SATAN: Leaking Government Websites’ Data And Threatening Others
April 14, 2020, Kathmandu
After three days of unavailability on Twitter, SATAN (@satan_cyber_god) tweeted a tweet yesterday. After his return to Twitter, he started posting the website bugs and warning them to fix it as soon as possible. He also leaked the login credentials of some government websites through his twitter handle.
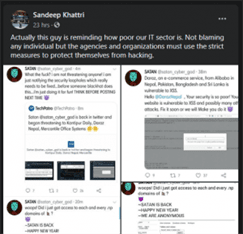
He tweeted threatening Kantipur Daily, a pioneer news media in Nepal. In his tweet, he stated that Firebase JSON file’s permission is not set properly in Kantipur Daily’s website. He added, if they don’t fix it, he has to.

In his other tweet, he informed Daraz that its site is vulnerable to XSS and possibly more attacks. He then warned them to fix it soon else he would make them fix it.

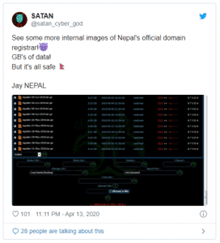
The things got worse when he tweeted the picture saying he was in Mercantile’s system then. He challenged it to do whatever it wanted to do. In case you didn’t know, Mercantile is the official registrar of .np domains. It registers all .np domains.
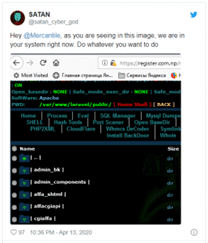
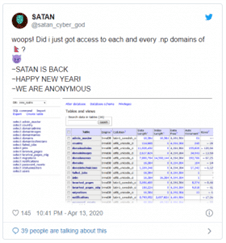
After a short time, he again tweeted on the same case. He tweeted saying, “woops! Did i just got access to each and every .np domains of Nepal?” In the same tweet, he uploaded the picture of the database of .np domains.
Then, he retweeted the tweet of TechPatro, a tech news portal of Nepal, in which it had said that SATAN was threatening Kantipur Daily, Daraz and Mercantile by saying that he didn’t threaten anyone. He added he was just informing the companies before a black hat exploits the loopholes and harms the website and was doing for fun. He then warned to think before posting such things again.
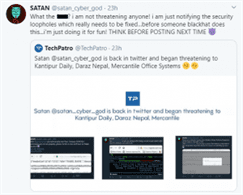
TechPatro responded to its tweet saying that he leaked CTEVT information which can harm a lot of people and recent data breaches triggered phishing attempts to many Viber users recently. After some time, TechPatro noticed a login attempt to its system with a fake IP address of Beijing.
He then added a photo saying, “See some more internal images of Nepal’s official domain registrar! GB’s of data! But it’s all safe.”
After some time, he shared the login credentials of some government websites and asked if people still take him as a joke.
The last tweet of the day threatened Nepal Electricity Authority, an electricity supplier of Nepal. He said, “Nepal electricity authority <3 you will be notified tomorrow!”. He added, “Thanks for the support! Hope we can bring the change together <3”. His tweet ended with “ Operation #Justicefornirmala soon” which suggests people associated with the Nirmala Pant rape and murder case are his next targets.
What do people say about his activities?
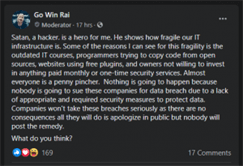
Currently, people in social media are divided into two groups. The first includes people who are criticizing his deeds. They say that the path followed by him is completely wrong. They believe he should better inform the management team about the bugs than posting it public online. They believe he’s a newbie to hacking and should use his skills legally.
The next sort people are appreciating his activities. Some of them even publicly say that he’s their hero. According to them, he’s doing what he’s supposed to. They say that he’s showing how fragile our IT sector is.
Whatever people say, the path he’s followed is definitely wrong. He needs to understand that his activities are illegal. He should inform the website developers about the bugs. He shouldn’t post these things on social media. He even shared the login credentials of some government sites through his tweeter handle. We’re against his ways of expressing website vulnerabilities. He should stop doing these things and turn himself as a white-hat hacker helping websites fix their issues.
We also suggest Nepalese websites introduce bug bounty so that ethical hackers get motivated to report the website about the vulnerabilities. They must fix the vulnerabilities as soon as possible to decrease possible attacks on the site.