Google patches Chrome zero-day, eighth one in 2021
19th July 2021, Kathmandu
Eight security vulnerabilities, including a high severity zero-day flaw exploited in the wild, are inscribed by Google Chrome.
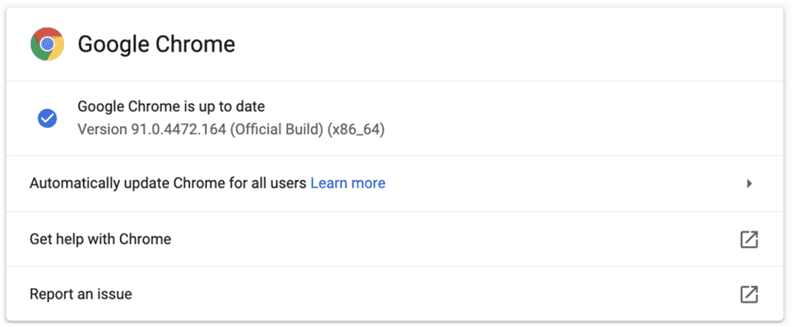
Chrome’s new version (91.0.4472.164) has been released for Windows, Mac, and Linux to patch for a total of 8 security vulnerabilities. As yet, limited information, such as CVE identifiers and vulnerability types, on the currently uncovered vulnerabilities was done by Google.
It also reported that among the eight vulnerabilities CVE-2021-30563 is a zero-day and actively used in the wild with a known exploit for it.
Following are the lists of eight vulnerabilities along with some details:
- CVE-2021-30541: Use after free in V8
- CVE-2021-30559: Off-limits Write in ANGLE
- CVE-2021-30560: Apply After Free Blink XSLT
- CVE-2021-30561: Type Confusion in V8
- CVE-2021-30562: Use After Free in WebSerial
- CVE-2021-30563: Type Confusion in V8 (Zero-Day)
- CVE-2021-30564: Heap Buffer Overflow in WebXR
Additional information on the tools for analyzing these vulnerabilities was shared by Google. The given below is a list of the tools used by Google for bug detection:
- AddressSanitizer
- MemorySanitizer
- UndefinedBehaviorSanitizer
- Control Flow Integrity
- libFuzzer
- AFL
Effect:
Successful exploitation by a remote attacker on CVE-2021-30541 by causing heap corruption in V8 through a crafted HTML page is able to execute arbitrary code and gain full control of the system.
Impact Summary CVE-2021-30541
Category: Use After Free
CVSS 3.1 Base Score: 8.8 High
CVSS 3.1 Vector: AV: N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Successful exploitation by a remote attacker on CVE-2021-30541 by performing outbounds memory access in ANGLE could gain unauthorized access on the system that leads to an information leak.
Impact Summary CVE-2021-30559
Category: Use After Free
CVSS 3.1 Base Score: 8.8 High
CVSS 3.1 Vector: AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Successful exploitation by a remote attacker on CVE-2021-30559 by causing heap corruption in Blink XSLT through a crafted HTML page, could perform arbitrary code and gain full control of the system.
Impact Summary CVE-2021-30560
Category: Use After Free
CVSS 3.1 Base Score: 8.8 High
CVSS 3.1 Vector: AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Successful exploitation by a remote attacker on CVE-2021-30560 by making heap corruption in V8 through crafted HTML page, could perform arbitrary code and gain full control of the system.
Impact Summary CVE-2021-30561
Category: Use After Free
CVSS 3.1 Base Score: 8.8 High
CVSS 3.1 Vector: AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Successful exploitation by a remote attacker on CVE-2021-30561 by making heap corruption in WebSerial through a crafted HTML page, could execute arbitrary code and gain full control of the system.
Impact Summary CVE-2021-30562
Category: Use After Free
CVSS 3.1 Base Score: 8.8 High
CVSS 3.1 Vector: AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Successful exploitation by a remote attacker on CVE-2021-30563 by making heap corruption in V8 through a crafted HTML page, could execute arbitrary code and gain full control of the system.
Impact Summary CVE-2021-30563
Category: Use After Free
CVSS 3.1 Base Score: 8.8 High
CVSS 3.1 Vector: AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Successful exploitation by a remote attacker on CVE-2021-30564 by causing heap corruption in WebXR through a crafted HTML page, could execute arbitrary code and gain full control of the system.
Impact Summary CVE-2021-30564
Category: Use After Free
CVSS 3.1 Base Score: 8.8 High
CVSS 3.1 Vector: AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Solution (Update)
Google Chrome needs to be updated to the stable version 91.0.4472.164 to possibly defend against such attacks.