BRAC Bank Relies on Trend Micro’s Cybersecurity Solutions to Prevent APTs
April 09, 2020, Kathmandu, Nepal
Trend Micro Inc, a global leader in cybersecurity solutions, announced that it is providing a comprehensive suite of cybersecurity solutions to BRAC Bank Ltd., a Bangladesh-based bank...
A Brief History Of Internet Security, Technology Hit The Market
History of information security. From the ancient day's communication, military captains and diplomats knew the essence to have specific methods to protect the confidentiality of correspondence and have some mechanism to detects...
Which Physical Security Measure Is In Place ?
You are testing physical security measures as part of a pen test team. Upon entering the lobby of the building, you see the entrance has a guard posted at the lone...
Top 7 Cybersecurity Companies in Australia
2nd Feb 2021, Kathmandu
Cybersecurity is the practice of protecting computer systems and networks from malicious attacks. With the digital revolution and the increased reliance on computers and computer systems, cybersecurity has...
Facebook Hack Exposed Accounts Of 50 Million Users
On Friday night Facebook admitted that hackers attacked it. As stated in the company’s blog spot, the pirates had exposed the data of nearly 50 million users.
Reportedly, Facebook was already notified...
Are You Using SMS For Two-Factor Authentication? Here’s Why You Should Stop
April 13, 2020, Kathmandu
There’s always a negative side to something good. Using two-factor authentication, or 2FA also has a downside. You might risk getting codes over SMS or text message.
The coronavirus...
How Protected Is Your Organization From Cyber Attack?
May 31, 2020, Kathmandu
In today's digital age, Cyber Security has increasingly been critical. Cybersecurity challenges has been national security. Organizations, government, and private entities, individual's confidential information, all has been prone...
Basic Information Security Concepts, Dilli Sharma
Fundamentals concepts on Security Policies and Access Control in Computer Security
Terms-Computer security, network security, Internet security, and information security are interchangeably used in the fields of security in computing.
The computer security...
Apple Release Emergency Security Patch IOS 9.3.5
1st September 2016, Kathmandu
Apple was bound to release iOS 9.3.5 update “Emergency” Patch for apple products like iPhone, iPad, etc. after advanced spyware targets the iPhone used by a renowned UAE...
Learn To Protect Your Organization From Spear Phishing
Spear Phishing is the fraudulent attempt to obtain sensitive information such as usernames, passwords, and credit card details (and money), often for malicious reasons, by disguising as a trustworthy entity in electronic communication. The word is a neologism created as a homophone of fishing due...
Cybercrime Community Awareness And Prevention, CSI Nepal
26th Cyber Security Training has been successfully conducted at Chitwan municipality-7, Gunjanagar, Chitwan. In the program, Dr. Ramhari trained the trainees through Skype.
Considering the increasing threats revealed due to the development...
Tips To Keep Children Safe Online
As we know, most of the people and children spend a lot of time on the internet or social networks these days. It provides a convenient way for them to explore...
API Risks: What are They and How to Manage Them
24th April 2021, Kathmandu
API security risks are a common problem in today’s cyber world. Unfortunately, cyberattacks have become an everyday word in today’s vernacular. Like any software, APIs can be compromised...
Ways To Prevent Cyber Attacks – Nepal Vulnerable To Cyber Attacks
September 18th, 2019, Kathmandu
Internet is used to access public network while keeping your details confidential and secure. We do everything on the internet – from the banking business, online shopping, etc....
Evaluation of Railway Tender Stopped After The Bidding Was Hacked
30th August 2020, Kathmandu
The website of the Public Procurement Monitoring Office (PPMO), bolpatra.gov.np, was hacked while evaluating the bids for the disputed railway construction contract.
According to a notice issued by the...
Webinar Spamming Incidences Increase in Nepal
Kathmandu, May 3rd, 2020
Schools, colleges, and various institutions have been hosting webinars to make the best use of the lockdown period after the COVID-19 crisis began. Girls In Tech - Nepal, in...
India’s Largest eLearning Platform Unacademy Hacked
9th May 2020, Kathmandu
India’s largest eLearning platform Unacademy is hacked. The information of users is put up for sale.
Unacademy is an educational platform with a massive user base. It is the...
Android Users At High Risk During Coronavirus Outbreak
Kathmandu, March 29
Watch out Android Users! The ongoing COVID-19 pandemic is proving to be an opportunity for cyberattackers to stage cybercrime. The attackers launch malware attacks, phishing campaigns, create scam sites...
Cyber Security Bootcamp and Training Conducted Successfully At Pokhara
September 4th, 2019
A training on ‘Cyber Security - Securing Business in the 21st Century was organized by Annapurna Software Development in association with One Cover Private Limited at Hotel Barahi Pokhara...
WPA3 ensuring a secured and hack-proof Wi-Fi connection
WPA3 is ensuring a secure and hack-proof Wi-Fi connection. Wi-Fi nowadays is hacked very often, and a lot of people are quite distressed about it to solve this the Wi-Fi alliances...
Social Engineering psychological manipulation of its Types
Social engineering is a non-technical method of intrusion hackers which relies heavily on human interaction and often involves tracing people and breaking standard security procedure. It is one of the significant...
National Cybersecurity Awareness In Rehabilitation Center
Awareness about cyber security at Hope Foundation. CSI Nepal completed its awareness session at Hope Foundation located at Kapan, Kathmandu. The program started at around 7 AM with Mr. Chiranjibi Adhikari and...
3 Possible Alternative Ways To Protect USB Pen Drive With Password
Today many of us are using Pen drive to keep our data and information, so there is always the risk of being known by others if mistakenly you forgot or lost...
Garima Development Bank Launches ‘Be Careful’ Campaign
30 March 2021, Kathmandu
The threat from cybercriminals has increased drastically in Nepal. Just the other day, Deepa Shree Niraula and Saroj Khanal’s Facebook Account has been hacked.
Garima Development Bank has launched...
Tiktok Tracked Users’ Data For Over A Year
14th August 2020, Kathmandu
According to the Wall Street Journal, Tiktok tracked Android users’ data for over a year until November 2019. This is yet another blow for tiktok in the recent...
Use Of Honeypots For The Security Of IoT
December 15, 2019, Kathmandu
Honeypots can be defined as a computer security mechanism which detects, deflect, counteract attempts at unauthorized use of information systems.
There are basically two types of honeypots based on...
Hacker Targets Whats App- Reports
Recently hackers have made an attack on Facebook and exposed the data of 50 million users. Reportedly, like Facebook Whatsapp is also in high risk of being attacked.
The new published by...
Apple Has Become The Most Used Brand For Brand Phishing
April 16, 2020, Kathmandu
Apple has always been a leading technology market. In the history of nearly 45 years, the company has gained a lot of good reputation and bad ones. A...
Nepal’s First Cybersecurity Journal Has Been Launched
6th October 2021, Kathmandu
Nepal’s first Cybersecurity Journal has been announced in an event today. Journal of Cyber Security Research and Innovation (Journal of CSRI) is a peer-reviewed interdisciplinary journal on Cyber...
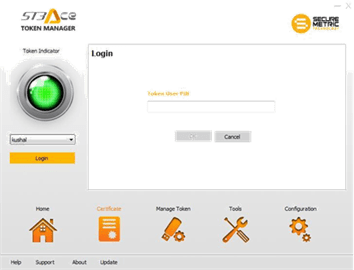
FAQs: Guidelines For Usage Of Digital Signature In Nepal
Steps for Using Tokens from Nepal Certifying Company (NCC)
Insert the Nepal Certifying Company Pvt. Ltd. provided token, Wait for the dialogue box to appear.
Click on the Open folders to view files,...