Top 9 Causes Of A Server Down Or Server Crash
Another massive attack at Nepal Government Servers. This is wake up call for those who are envisioning digital Nepal. In a client-server architecture, a server’s responsibility is always to serve its...
Mobile Device Security Best Practices You Should Know
21 July 2021, Kathmandu
These days proximately everyone has a mobile contrivance. You assuredly can’t get along in society without a perspicacious phone to avail you check scores, message your friends, make...
DDoS Attacks in Russia Surge 2.5 Times in 2021
23rd October 2021, Kathmandu
Russian state-supported danger entertainer bunches are known for inventive assault procedures and malware attacks, administering the underground darknet markets with different cybercriminal exercises.
Russian aggressors have expanded their objectives...
Bugs in Managed DNS Services Cloud Let Attackers Spy on DNS Traffic
12th August 2021, Kathmandu
Cybersecurity researchers have disclosed an incipient class of susceptibilities impacting major DNS-as-a-Accommodation (DNSaaS) providers that could sanction assailers to exfiltrate sensitive information from corporate networks.
"We found a simple...
New MySQL Zero Days Exploits To Hack Databases
It’s tough to find a single day; the hacking issues did not hear. Every day we face many cyber crime-related problems and solving those had become a tough task. This time...
Cisco Issues Critical Fixes for High-End Nexus Gear
28th August 2021, Kathmandu
Networking giant issues two critical patches and six high-rigor patches.
Cisco Systems relinquished six security patches tied to its high-end 9000 series networking gear ranging in paramountcy from critical,...
Fraud Alert; Scammers Using the Name of Khalti to Scam Users
18th May 2020, Kathmandu
Some scammers are using the name of Khalti to scam Khalti users. This news came to light recently.
The digital wallet company Khalti has a wide audience and a...
Letter from Assistant Professor of Cyber Security Dr. Ramhari Subedi
Hello everyone,
Cyber Security International (CSI) is based out of Washington DC USA. CSI mission is to raise awareness of emerging cyber threats to teenagers’, parent, students, officials, social activists, leaders, lawmakers,...
How Microsoft Windows 10, 11 Serious SAM Vulnerability can be Mitigated?
28th July 2021, Kathmandu
Microsoft Windows 10 and Windows 11 users are at risk of new unpatched vulnerabilities that have recently been publicly disclosed.
As we reported last week, the vulnerability SeriousSAM allows...
Scam Links Circulating in the Name of Bhatbhateni Supermarket
21st October 2022, Kathmandu
A scam link has been circulating in the name of Bhatbhateni Supermarket. Scam links are being spread on social networking sites and the internet saying that a new...
IT Risk Management Audit And Assurance Application
IT risk management is the application of the risk management methodology of information technology so that the IT risks could be managed. It can be taken as a component of greater...
Creator of Zero-Trust Model Says Trust Did Not Exist in a Digital World
31st October 2021, Kathmandu
It appears to be no security gathering or discussion is finished without a conversation on zero trust. However, not very far in the past, "trust" was just a...
67% Indians find no Harm in Slow down of Software Updates: Report
24th May 2021, Kathmandu
While cybercrimes are on the growth, 67 percent of Indian clients think there is no harm in delaying software updates, giving hackers enough time to break into their...
McAfee Reveals Potential Risks in Online Streaming of Popular Entertainment Titles
26th June 2020, Kathmandu
The world is experiencing a surge in internet and data traffic with stay-at-home orders in most countries. Specifically, there has been a rise in the consumption of online...
A Wide Range of Cyber Attacks Leveraging Prometheus TDS Malware Service
6th August 2021, Kathmandu
Multiple cybercriminal groups are leveraging a malware-as-a-accommodation (MaaS) solution to distribute a wide range of malevolent software distribution campaigns that result in the deployment of payloads such as...
“Wasted” WiFi Signal Powers Small Devices
28th May 2021, Kathmandu
This article is freely split under the Attribution 4.0 International license. Researchers have developed a way to gather energy from WiFi signals to power small devices.
The amount of...
Ever thought of a hack-proof Computer? Some Researchers Are Working
22nd May 2021, Kathmandu
Computer security is becoming increasingly significant due to the increased reliance on computer systems, the Internet, and wireless networks.
Ever thought of a hack-proof computer? Some researchers are working...
Peekaboo Zero-Day Vulnerability Permits Hacking Of Surveillance Cameras
Security cameras of IoT that represents various vendors invite opportunities for flaws. Recently, researchers have discerned a similar vulnerability that lets the hacking of surveillance cameras. By employing this “Peekaboo zero-day vulnerability”...
ChildSafeNet and UNICEF Publish White Paper on Cyber Safety
10th Feb 2021, Kathmandu
Observing the Safer Internet Day 2021, ChildSafeNet and UNICEF Nepal published a white paper on protecting children and young people online, on 9 February 2021.
The white paper includes...
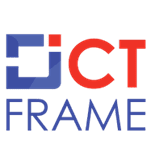
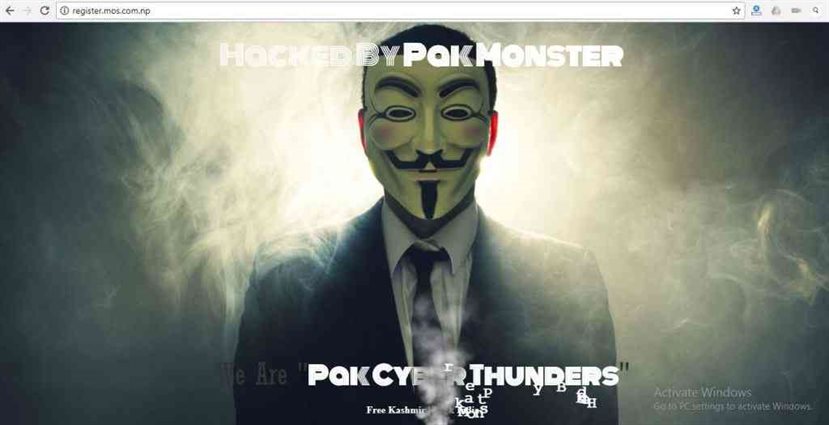
Mercantile server has been hacked by Pakistani Hacker
Mercantile server has been hacked by Pakistani Hacker called PakMonster.
Anti-Rape System Developed By Nepali Youths, Watch The Video
12th October 2020, Kathmandu
With the ongoing increase in rapes around the country, it has been hard for all the females to walk freely in the streets, with keeping the constant fear...
User Guide To Digitally Sign Email Using Thunderbird Mail
Basic description for how to sign email using a certificate-based digital ID to allow others to sign using a certificate in Thunderbird Mail Version 38.5.1 or above.
Email Signing In Thunderbird Mail
Pre-requisites
...
Use Of Pornography Contents By The Children: A Major Concern During The Lockdown
April 10, 2020, Kathmandu, Nepal
Due to lockdown, many people are staying at their home and scrolling over the Internet. Small children whose schools are shut down are feeding over what they...
6 Fundamental Skills Required Pursuing a Career in Digital Forensics
22nd September 2021, Kathmandu
Digital forensics is a better career path to grow in 2021 and beyond. The cybercriminal's malicious activities are giving trouble to the digital forensics specialists. Attackers these days...
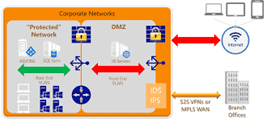
Building Secure Data Access,Threats And Countermeasures
The network security contains the policies taken to monitor and prevent misuse, access, modification or denial of a network accessible resources and computer network. Network security includes the authorization of access...
Ransomware Incident at Cloudstar Disrupts the Real Estate
21 July 2021, Kathmandu
A highly sophisticated ransomware incident at Cloudstar disrupts real estate. A highly sophisticated ransomware attack at Cloudstar, a cloud hosting service and managed service provider for varied real...
User’s not Accepting Privacy terms to face Limited Functionality: WhatsApp
19th May 2021, Kathmandu
What’s App has removed the May 15th finishing date for accepting the new privacy policy. In fact, the social messaging app now says the user will not lose...
Data of Two Million Users Leaked of Indonesia’s BRI Life
1st August 2021, Kathmandu
Indonesia’s BRI Life, the insurance arm of Indonesia's Bank Rakyat Indonesia (BRI), told that it had been inspecting affirms that the private details of over two million of...
Facebook Hack Exposed Accounts Of 50 Million Users
On Friday night Facebook admitted that hackers attacked it. As stated in the company’s blog spot, the pirates had exposed the data of nearly 50 million users.
Reportedly, Facebook was already notified...
How to Snoop With Kali Linux on Bluetooth Contrivances
10th October 2021, Kathmandu
Bluetooth has become a major component of our lives. Bluetooth contrivances are utilized every day by many individuals around the globe. Most of them, though, have no conception...